Featured
Table of Contents
What Is Openvpn?
Still, it deserves discussing that SSTP is natively constructed into Windows platforms, so it's much easier to establish than Open, VPN. Overall, both Open, VPN and SSTP are a decent choice, but Open, VPN is just more effective. In case you 'd like to discover more about SSTP, examine out this article.

It's safe to state that both Open, VPN and Soft, Ether are truly protected protocols. They're open-source, use military-grade ciphers like AES, make use of 256-bit file encryption, and likewise use SSL 3. The main distinction in between them is the age Soft, Ether is much newer than Open, VPN.
In terms of speed, Soft, Ether fares much better than Open, VPN. according to the research from the University of Tsukuba (the people behind Soft, Ether VPN, so not a 100% subjective source), the Soft, Ether procedure is expected to be 13 times faster than the Open, VPN protocol.
Comparing Openvpn Vs. L2tp/ipsec [Ultimate Blog]
You should understand that even if you use a VPN service provider who uses Soft, Ether connection, you'll still require to download extra software for it to run. With Open, VPN, that's optional. Like Open, VPN, Soft, Ether can also run its own server, but the Soft, Ether server can really run the Open, VPN protocol, alongside other protocols like IPSec, L2TP/IPSec, SSTP, and Soft, Ether.
In the end, Soft, Ether is a strong Open, VPN alternative. If for whatever reason you can't use Open, VPN, you ought to attempt Soft, Ether.
You need to be more cautious with IPSec when configuring it, since a little error can destroy the defense it offers. Considering that IPSec occupies kernel space (the space on the gadget scheduled for the operating system), its security can be restricted by the method it's set up by the supplier.
Understanding Vpn Protocols: Openvpn, L2tp ...
Still, you must understand that IPSec may take longer to work out the tunnel than Open, VPN does. Intrigued in discovering more about IPSec? Have a look at this short article. Open, VPN and IKEv2 are both safe and secure procedures, but it's worth noting that Open, VPN uses TLS/SSL to secure information at the Transportation level, while IKEv2 secures data at the IP level.
And while IKEv2 was developed by Cisco together with Microsoft, that's not such a substantial problem since there are open-source applications of IKEv2. Open, VPN uses more assistance when it pertains to cross-platform compatibility, but IKEv2 is typically a favorite of mobile users because it's natively integrated into Black, Berry gadgets.
What does that suggest? That if, for example, you were to change from a Wi, Fi connection to your information prepare connection on the go, IKEv2 might deal with that without dropping the connection. That, you ought to know that IKEv2 tends to be faster than Open, VPN, however it's likewise easier to obstruct than the Open, VPN procedure.
What Is Openvpn?
If you type "What is Open, VPN?" into an online search engine the results may lead you to think it's strictly an open source task. Yes, it is that, however it's not just that. The more accurate answer is that Open, VPN is the name of: An open source job we call Neighborhood Edition. Our tunneling procedure.
The Open, VPN Community Edition (CE) is an open source Virtual Private Network (VPN) task. It creates safe and secure connections over the Web using a custom-made security protocol that makes use of SSL/TLS. This community-supported OSS (Open Source Software) job, using a GPL license, is supported by lots of Open, VPN Inc. developers and contributors in addition to the prolonged Open, VPN community.

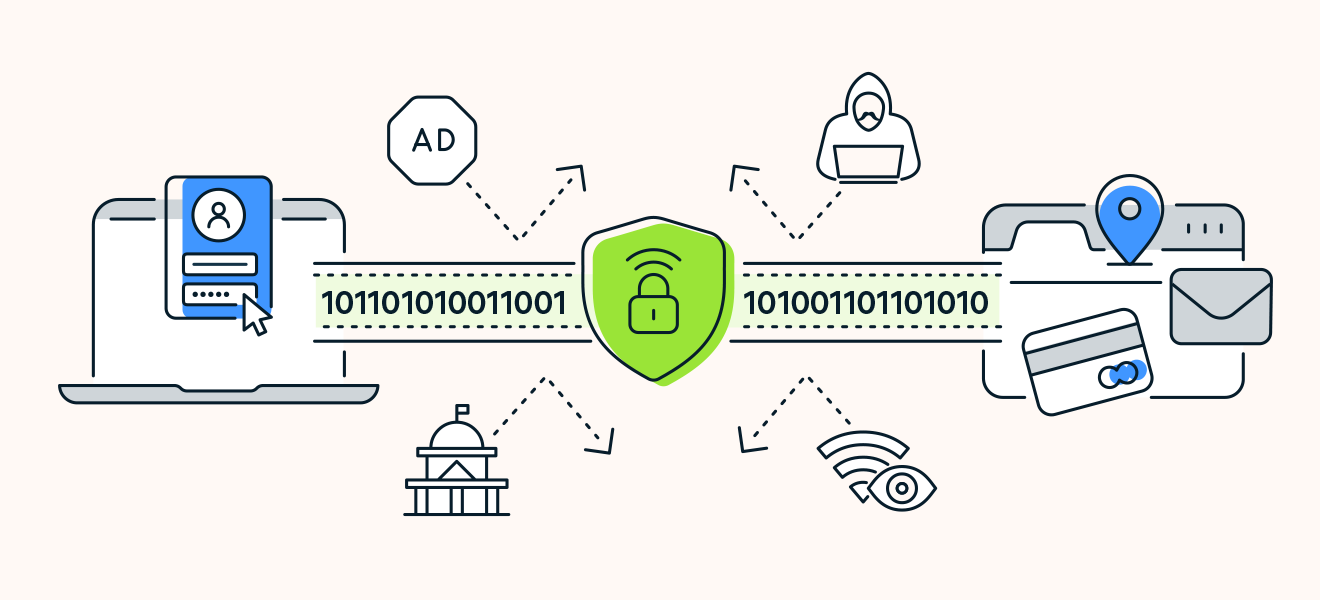
Open, VPN is an open source connection procedure used to assist in a safe and secure tunnel between two points in a network. In layman's terms, this implies that it is a trusted technology used by lots of virtual private networks, or VPNs, to ensure any information sent over the web is encrypted and personal.
Le Vpn Protocols – Openvpn
It's not uncommon to go to a VPN website and see them boasting about the reality that they use Open, VPN as a function.
No single tool or encrypted connection to the internet can guarantee your security and privacy, and Open, VPN is no various. There are good factors why it is considered one of the most secure connections, which we'll cover below.
Some of the links in this short article are affiliate links, which suggests that at no additional cost to you, I might be compensated if you select to utilize a few of the services listed. I only recommend what I personally use and I hope that the totally free information provides worth to you! Before we dive deeper into responding to the concern "what is Open, VPN" and how it works, let's take a step back to make sure we're clear on what a VPN protocol is.
Dispelling Myths: Openvpn Is Obsolete
If you leave your house to go out to consume, there are particular things you will think about: the security of the course, the ideal mode of transportation, what you need to take with you, and so on. Similarly, when data travels through a channel, it follows particular rules. And there isn't simply one set of rules to follow.
Perhaps you've heard of these protocols before. They usually go by an acronym such as: Point-to-point tunneling protocol Layer 2 tunneling protocol Web key exchange variation 2 Safe socket tunneling procedure, What is Open, VPN when compared to each of the protocols noted above? There's truly one huge difference: It is open source.
Latest Posts
8 Best Vpns For Small Businesses In Jul 2023
Best Vpns For Small Businesses (2023)
15 Leading Vpn Software For Startups For 2023