Featured
Table of Contents
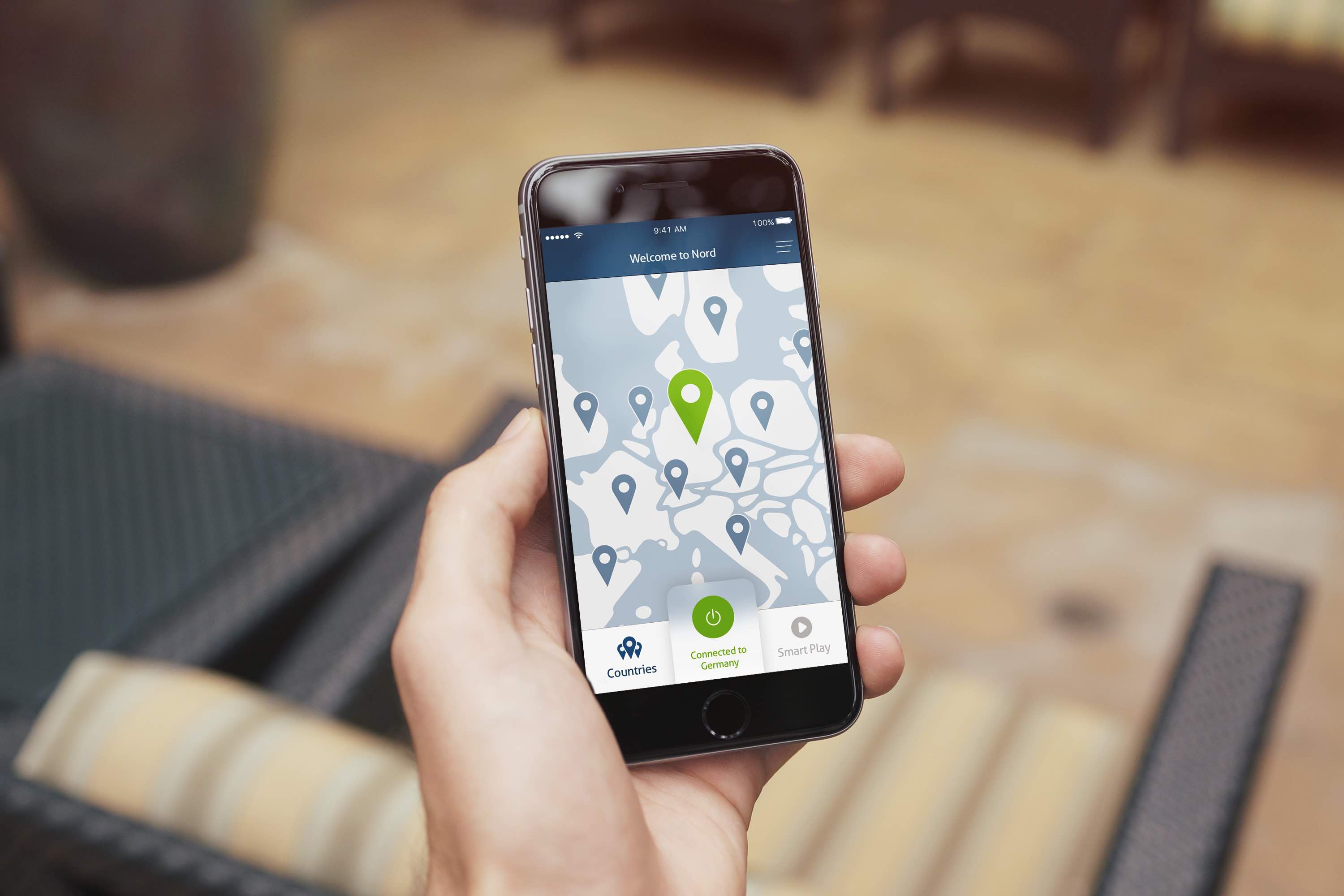
9 Best Business Vpns For Work In 2023
Another aspect to consider in selecting a VPN is how strong the file encryption is. More powerful file encryption is more difficult to break and provides better security. 256-bit file encryption is basic in the VPN market, although some companies use less-secure 128-bit encryption. Check the company's website under the "functions" area, and they need to promote what level of file encryption they use.
To see how lots of are on deal, look for an area on the service provider's site titled "Server List" or similar - what are some factors to consider when choosing a vpn provider. This must reveal you a total list of all the servers that are offered and their locations. Generally speaking, more servers is much better as it offers you more options to discover a quick and trusted server when you link.

Just look for a service provider with at least 500 servers which must be sufficient for many people. You will also wish to inspect the number of countries servers are readily available in. You can use a VPN to get around local restrictions as long as your supplier has a server in the nation you want to access the web from.
The Ultimate Beginners Guide To Vpns
One drawback to utilizing a VPN is that it can slow down your web connection a little due to the extra file encryption action that the data goes through. To lessen this slowdown, you'll want a VPN that has quick servers. It can be tough to find out how quickly a VPN will be.
You can look up VPN evaluations which typically include a speed test, but bear in mind that your experience will be different from someone else's. This is because the speed of your connection will depend upon both where you are located and where the server that you are linking to is located.

Numerous VPN providers use a free trial or a money-back guarantee to attempt out their servers for a couple of days and see if you are pleased with the speeds before dedicating to one company. Before you choose, you can likewise examine what optional functions a VPN supplier uses by inspecting their site.
Beginner's Guide To Vpn - Everything You Need [5000+ ...
They are the core innovation that determines how your data is routed to the VPN server. There are a range of significant VPN procedures, and they are not developed equivalent. You should check which VPN protocol a supplier supports. Do not fret if you aren't skilled with VPN procedures. We have a thorough comparison of the significant VPN protocols to make it simple for you to put whatever in viewpoint.

Take the time to find the right VPN for youstart with our guide to the very best VPN services. If you're not exactly sure where to begin, we recommend Express, VPN or Private Internet Gain Access To. Follow our links and minimize a membership!.
At minimum, we can presume all users have the very same IP address (due to being connected to the exact same server) and for that reason have the exact same "exit node." This makes it harder for the various websites, web services, or web apps to select out who is who, even if multiple users go to the exact same website at different times (what are some factors to consider when choosing a vpn provider).
What Is A Vpn And Why Do I Need It?
In many cases, complimentary VPN providers have shared information with cloud suppliers, federal governments, and anybody happy to provide some money in exchange for the data; they have likewise been accused of utilizing gadget resources, such as CPU power, to mine crypto on their own (cryptojacking)! Among the most crucial things to try to find in a VPN service provider is the contents of their information personal privacy - specifically information collection and any possible retention of gathered data - policies.
If the VPN provider collected PII, then these logs might be used and connected back to a user's true identity. It's frequently worth digging much deeper than what the marketing claims (or easily leaves out) on the VPN supplier's website, thinking about concerns such as: Does the VPN provider use a publicly available audit of their no-logs claims? Is an audit on a VPN service provider's no-logs policy conducted routinely?
To relieve this, trusted VPN service providers frequently offer alternative forms of payment - or perhaps anonymous payments. Alternative forms of payments, such as accepting Bitcoin or Litecoin, aren't constantly confidential; normally anonymous payments include accepting Monero cryptocurrency and cash. Depending on the user, this may not be an area of fantastic issue.
Private Internet Access: The #1 Best Vpn Service For 10+ Years
With open-source customers, anyone can check the source code for any factor. Open-source customers generally also reveal a commitment to contributing to the open-source community. Tweaks/adjustments can be more easily done or recommended by users ready to do so. If the VPN supplier's clients are not open-source, then it's encouraged to For instance, does the VPN customer app collect any device information? Does the client have embedded trackers? Authorizations such as bluetooth and area services gain access to should be concerned with suspicion as they are not required to render VPN services.
Procedures Procedures are the engine behind VPN connections. Traditionally, centralized VPN suppliers use numerous procedures; the user typically chooses which protocol to utilize. A couple of various VPN procedures exist and there is no "best" service; VPN suppliers should offer a minimum of User requirements and requirements typically determine which protocol to choose over the others (what are some factors to consider when choosing a vpn provider).
Latest Posts
8 Best Vpns For Small Businesses In Jul 2023
Best Vpns For Small Businesses (2023)
15 Leading Vpn Software For Startups For 2023