Featured
Table of Contents
What's The Difference Between Vpn & Ip Vpn?
Believe of your internet connection as a tunnel. This tunnel is covered in a layer of encryption that keeps others from seeing what you're doing online. If you're visiting to your Twitter account, for example, you're passing your account information from your computer system to Twitter through a tunnel that nobody else has access to.
Link to your VPN, run the tests on one or both websites and validate that the info is different.
Now that you understand what a VPN is, it's time to choose one. The very best VPN services fire on all cylinders, using security, personal privacy, ease of use and a huge choice of servers. Here are a couple of things you should look for when choosing a VPN: VPNs use an encrypted channel for your information, however that does not imply the VPN itself can't log your individual details.

Unless you're under ISP throttling, a VPN will slow down your web connection. Some VPN services slow down your speed more than others.
What Is A Vpn? How Does It Work And Why Do You Need ...
VPNs are legal in most nations. Although not technically unlawful, some countries are more stringent when it comes to VPN users, so it's finest to speak with the laws in your region. Regardless, doing anything prohibited while connected to a VPN is still prohibited. Contrary to what some may inform you, you can be tracked while utilizing a VPN.
3 each month for each user. Finest UK VPN Solutions We've assembled a list of what we believe are the best VPNs for 2023.
This means your Internet Service Supplier (ISP) and other 3rd parties can not see which websites you visit or what information you send and receive online. A VPN works like a filter that turns all your information into "mumbo jumbo". Even if someone were to get their hands on your information, it would be worthless.
Unencrypted information can be viewed by anyone who has network gain access to and desires to see it. With a VPN, hackers and cyber crooks can't decipher this data. To read the data, you need a file encryption key. Without one, it would take millions of years for a computer system to figure out the code in case of a brute force attack.
How Does A Vpn Work? Adguard's Complete Guide
: VPN servers basically act as your proxies on the web. In addition, a lot of VPN services do not save logs of your activities.
Providers and websites frequently include content that can only be accessed from certain parts of the world. Standard connections use regional servers in the nation to determine your location.
A VPN should also prevent you from leaving traces, for instance, in the kind of your internet history, search history and cookies. The file encryption of cookies is particularly essential because it avoids 3rd celebrations from accessing to secret information such as personal data, financial info and other content on websites.
At the internet level, regional networks and gadgets could be linked to the universal network and this is where the risk of direct exposure became clear. In 1993, a team from Columbia University and AT&T Bell Labs lastly prospered in developing a sort of first version of the modern VPN, called sw, IPe: Software application IP encryption procedure.
Beginner's Guide To Vpn - Everything You Need [5000+ ...
In the USA, Great Britain and Germany, the percentage of VPN users is, however is growing. Among the greatest drivers for VPN adoption over the last few years has actually been the increasing need for content with geographical gain access to constraints. For example, video streaming services such as Netflix or You, Tube make sure videos offered only in specific countries.

A VPN encrypts your surfing behavior, which can only be deciphered with the assistance of a secret. Just your computer system and the VPN know this secret, so your ISP can not acknowledge where you are surfing. Different VPNs use different file encryption processes, but typically function in three actions: As soon as you are online, start your VPN.
Your ISP and other 3rd parties can not find this tunnel. Your gadget is now on the local network of the VPN, and your IP address can be altered to an IP address provided by the VPN server. You can now browse the internet at will, as the VPN secures all your individual data.
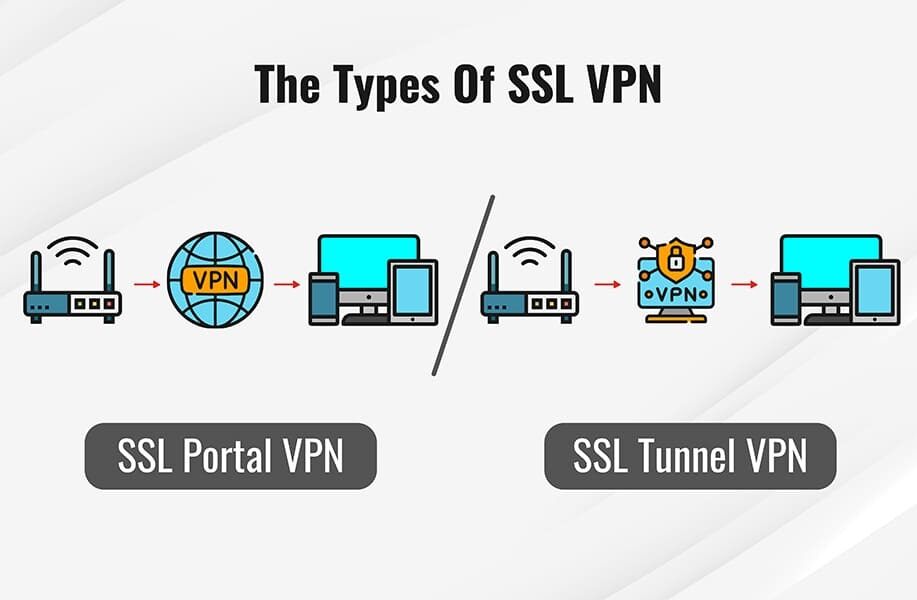
Site-to-site VPNs are primarily used in big business. They are complicated to execute and do not provide the very same versatility as SSL VPNs.
What Is Vpn? Virtual Private Networks 101
It prevents third parties from accessing and jeopardizing the network connection and secures information all the method to the company. It also avoids ISPs from accessing information that, for whatever reason, stays unencrypted and bypasses any constraints on the user's internet access (for circumstances, if the federal government of that country restricts web gain access to).
Offered a proper telephone system is offered, the employee can, for example, link to the system with a headset and act as if he/she were at their company work environment. Consumers of the company can not even tell whether the employee is at work in the business or in their home workplace.
Latest Posts
8 Best Vpns For Small Businesses In Jul 2023
Best Vpns For Small Businesses (2023)
15 Leading Vpn Software For Startups For 2023