Featured
Table of Contents
Tor Vs Vpn: Which One Should You Use?
Among the crucial differences between Tor and a Virtual Private Network (VPN) is who controls the tool., which indicates that they are centralized. If you use a VPN, you have to rely on that the VPN company will honor its dedication to keep your information safe and secure and private. In contrast,.

Tor, on the other hand, is slower and less easy to use. It's also a popular fact that Tor has been utilized for not-so-ethical activities.
Tor is not recommended for streaming as the connection is too sluggish. Yes, many VPNs are quickly enough for streaming.
Whonix ™ Versus Vpns
A lot of VPNs are simple to use and instinctive. Slow Quick speeds, however this will depend on the VPN supplier, the server you pick and your distance to it, and other factors.
Just those that have the secret to open this safe (which is you and the information's destination, like a site) can see your data. Thanks to modern-day encryption algorithms (or locks), it's near difficult to break into your information. Express, VPN uses an encryption algorithm called AES 256-bit, which is the same algorithm used by the government and armed force.
You will experience speed loss due to the fact that your information requires to travel further to get to its destination and because the file encryption process requires time. That said, this distinction is hardly visible with a premium VPN, and it won't affect your speed as much as Tor does, as Tor isn't enhanced for speed as some VPNs are.
Vpn, Proxy Or Tor: What's The Difference And What's Best?
This is why you need to try to find a VPN which uses an automatic kill switch, as it will disconnect you from the internet in case your VPN software stops working. Each node encrypts your data prior to it is forwarded to the next server. When your traffic is gotten by the last server (called the exit node), it's decrypted and sent to the website you're visiting.
The exceptions to this are the entry node, which can see your real IP, and the exit node, which unlocks your encrypted data. Spies can see your traffic once it leaves the network, however not where that information came from., including hackers and spies. Bad nodes typically harvest info such as login information to sites, individual details, online chat messages, and e-mails.
To protect yourself from bad relays on Tor, I recommend the following: over your connection. Never log into websites unless they utilize HTTPS. to secure your sensitive details and login information we'll speak about this in more detail below. For more details on this web browser and suggestions on how to stay safe while utilizing it, have an appearance at our Tor novice's guide.
Unmasking The Differences Between Tor And Vpn
Facebook has actually a. onion mirror site so that individuals in heavily-censored areas can utilize it to interact. The Tor internet browser or Android app, or Tails, the Tor operating system, or Onion Browser, the Tor i, OS app.
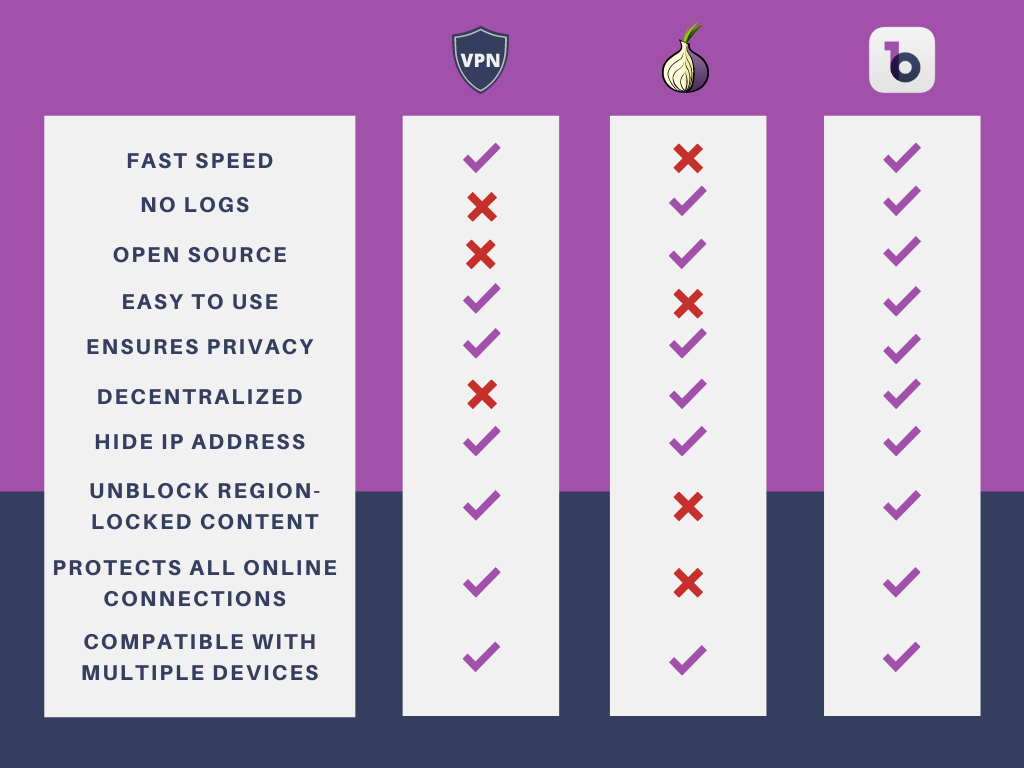
Since the browser hides your identity, Tor is frequently utilized to access global material in countries with rigorous online censorship. The Tor network is very slow, that makes it less than suitable for streaming, torrenting, gaming, or any other bandwidth-heavy activities. The exit nodes of Tor can be controlled by experienced people to spy on other users, so it's not as safe as a premium VPN would be.
, along with prevent your ISP and security bodies from spotting making use of Tor. This will also allow you to gain access to sites that obstruct Tor users. For this setup,. This technique needs more technical know-how because you'll require to configure your VPN client to deal with Tor.
Vpn Vs Tor, Which Is Better? - Bitvpn Blog
Although Tor's entry node can still see your real IP, your VPN will just see the exit node's address. Your ISP will not have the ability to see that you're connected to a VPN, but it can see that you're utilizing Tor. Since you can pick which remote server your VPN utilizes,, too.
Your traffic is not secured when it leaves the Tor network, so. You need to conceal your use of Tor from your ISP and monitoring bodies.
You desire to websites. Another option is to combine both and utilize Tor over VPN. Tor protects your privacy by routing traffic through multiple file encryption layers and relays, however your information is susceptible on the exit node. VPNs encrypt your internet traffic end-to-end and reroute it through remote servers of your choice while changing your IP address.
Tor Vs. Vpn: What's The Difference Between Them? ...
When you use Tor, your web traffic is encrypted and routed through numerous nodes, making it more difficult for your ISP to see what you're doing online. This can assist avoid ISP throttling based upon your online activities, such as streaming videos or downloading big files. , which implies that some ISPs may still be able to spot and throttle Tor traffic.
We advise Express, VPN the # 1 VPN out of over 350 providers we have actually checked. It has military-grade encryption and privacy functions that will guarantee your digital security, plus it's presently using 49% off.
Latest Posts
8 Best Vpns For Small Businesses In Jul 2023
Best Vpns For Small Businesses (2023)
15 Leading Vpn Software For Startups For 2023